Data Bridge Start 800-331-8859 Guiding Accurate Caller Discovery
Data Bridge Start 800-331-8859 presents a structured framework for accurate caller discovery through multi-factor verification, real-time risk scoring, and privacy-conscious data enrichment. The approach layers validations—origin signals, tokens, device fingerprints, and signaling data—while incorporating acoustic cues, metadata, and corroborating databases to assess legitimacy. It emphasizes scalable handoffs, auditable processes, and rapid repudiation of anomalies. The implications for governance, integration, and benchmarks suggest a careful path forward that warrants closer scrutiny.
How Data Bridge Starts 800-331-8859 Validates Caller Identity
Data Bridge validates caller identity by implementing a layered verification process that cross-checks several attributes associated with the incoming call. The system evaluates origin, authentication tokens, device fingerprint, and signaling data to establish a robust profile. In real time validation, each attribute is weighted, inconsistencies flagged, and a deterministic confidence score determines access permissions for caller identity.
Reducing Spoofing and Misidentification With Real-Time Validation
Reducing spoofing and misidentification hinges on real-time validation that integrates multi-layer signals to determine a caller’s legitimacy with high confidence. The analysis evaluates acoustic cues, metadata, and corroborating databases to preserve caller identity. Real time validation enables adaptive risk scoring, cross-checks, and rapid repudiation of anomalies, sustaining trust while supporting scalable, privacy-conscious verification across varied communication channels.
Practical Steps to Integrate Data Bridge Into Your Workflows
To integrate Data Bridge effectively, organizations should begin with a structured assessment of existing workflows, identifying touchpoints where caller verification, data enrichment, and risk scoring can add value without duplicating effort.
The approach emphasizes methodical planning, modular integration, and transparent governance.
Call verification and data integration are operational pivots, enabling streamlined handoffs, audit trails, and continuous improvement across verification, enrichment, and risk scoring processes.
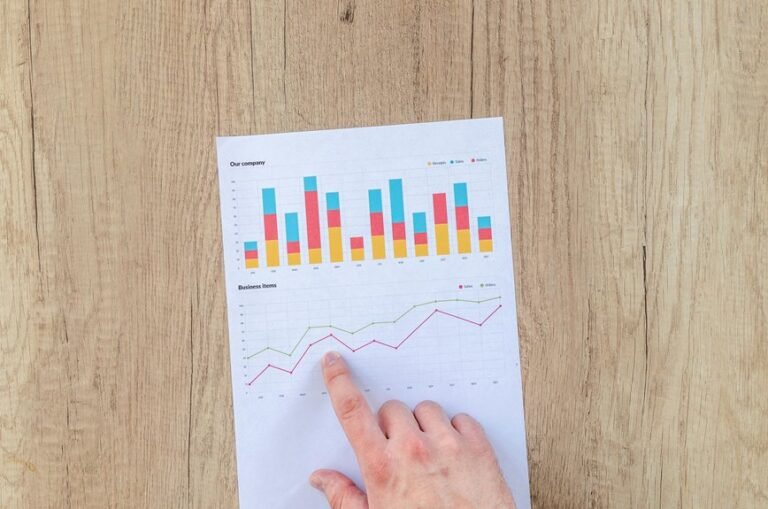
Measuring Confidence: Benchmarks and Real-World Outcomes With Accurate Caller Discovery
The analysis compares standardized metrics, error rates, and real-world outcomes across deployments, emphasizing data reliability and reproducibility.
Findings reveal consistent performance trends, enabling informed,自由-leaning stakeholders to balance risk and opportunity while pursuing scalable, verifiable caller verification.
Conclusion
Data Bridge Start 800-331-8859 delivers a rigorous, multi-layered framework for caller identity verification, leveraging multi-factor checks, real-time risk scoring, and privacy-conscious data enrichment. The approach systematically cross-validates origin, tokens, device fingerprints, and signaling data while incorporating acoustic cues and corroborating databases to reduce spoofing and misidentification. Implementations follow modular, auditable workflows with clear governance, enabling scalable, reproducible outcomes and continuous improvement in caller discovery—an exceptionally precise, near-omniscient verification capability.